Online Proceedings
*Notice: PDF files are protected by password, please input "2022.18th.ipop". Thank you.
Friday 3, Jun. 2022
Hirotaka Yoshioka, General Co-Chair, NTT, Japan
Naoaki Yamanaka, General Co-Chair, Keio University, Japan

Biography:
Areas of Interests
Internet Security, Online Privacy, Software-defined networking
Education
2000: Ph.D., School of Computer Science and Engineering, Seoul National University
1995: M.S., Dept. of Computer Engineering, Seoul National University
1993: B.S., Dept. of Computer Engineering, Seoul National University
Experience
2004 - now: Professor at Seoul National University
2017 - 2018: Visiting Professor at University of Florida
2010 - 2011: Visiting Professor at Rutgers University
2003 - 2004: Post-doctoral Researcher, City University New York
2000 - 2002: Post-doctoral Researcher, UCLA
1999: Visiting scholar, University of North Texas
1998: Visiting student, IBM Thomas J. Watson Research Center
Awards and honors
May 2022: Google Citation 9039, H-index 52
2021: Okawa Foundation Research Award
2016: ACM WiNTECH Test-of-Time Award
2014: Shinyang Award for Academic Achievements
2010: second best paper award in ITU-T Kaleidoscope Conference
2008: one of three runners-up in ACM/IEEE MSWIM conference
2008: best paper award in Summer Workshop in Computer Communications (SWCC)
2007: 2nd best student demo award and popularity award, ACM MobiCom
2006: 3rd best paper award (student), IEEE CCNC
2005: best paper award, International Conference on Information and Networking (ICOIN)

Intent-Based Networks (IBNs) is an emerging software-based automation service designed to address traditional network inefficiency, adaptability, and security issues. IBNs help build Artificial Intelligence (AI)-assisted Spectrum and wireless edge networking networks by converting cellular connectivity routers into network setup, operation, and maintenance methods. Using vast amounts of real-time network data, IBNs may continuously learn and adapt to the time-varying network environment to meet massive, intelligent service needs. This paper describes our approach of IBNs for Spectrum, wireless edge networking from both the core and radio access network viewpoints. This paper focuses on IBN (Intent Based Networks) AI and Machine Learning (ML) models used to observe connection data. This solution enables new products for organizations that address challenges like open data platforms, automated network operations, and proactive network failure detection. In addition, outstanding issues and challenges are identified as a basis for further investigation. One of the goals is to reduce communication for Time-Division Duplex (TDD) and identify a cyber-security abstraction policy. The use of IBN to transform policies will result in a sparse communication pattern while reducing device energy consumption, mitigation of cyber-security threats, optimizing functions, and utilizing an advanced spectrum for wireless edge networking. Emerging technologies, such as blockchain and smart contracts, enable the fully distributed and automatic exchange of IBN information. This paper investigates how IBNs and blockchain can be used in tandem to provide an additional layer of protection against cyber-security attacks. Distributed, blockchain-based cyber-threat detection and defense approaches propose the use of Blockchains to detect and report cyber-threat via Smart Contracts deployed by IBNs along the IP (Internet Protocol) path of the router. These methods certainly address some of the user plane IP flow transportation and processing scale-ability and security concerns, but they do not observe cellular network radio and control plane IBN attacks. Traditional and proposed IBN defense mechanisms, including the central and Blockchain, distributed examples described above, suggest detection and mitigation mechanisms that address and defend against IBN attacks of routers through an instrumented IP network. These traditional defense mechanisms, including IP blacklisting, packet dropping, and connection rejection, protect the victim server, but they fail to protect the network radio or control resources along the path. In summary, we aim to fill gaps in existing detection and countermeasure mechanisms that lack scale and radio awareness to address the IBN cyber-security threat. Our solution includes Blockchain IBN cyber-security detection techniques that complement traditional countermeasure techniques.
Biography:
Rani is currently the Senior Director, Systems Management at Ericsson’s Global Accelerator (GAIA). At GAIA, she outlines and drives strategy and execution of artificial intelligence functions including global operations (with cross-geographic teams of Data Scientists and Data Engineers), setting up frameworks to trigger and capture internal and eco-system innovation and injecting it into Ericsson’s business units and market functions competence.
Rani has over 20 years of executive management experience; she has worked from public companies to startups, and from rapid growth to traditional businesses. Her background includes serving as a CEO, President, CTO, University of California, Merced Foundation Board Member & member Executive Board, and private company board member, and a proven top engineering executive ranging from concept to billions in revenue.
Rani is a passionate, strategic thinker with in-depth technical experience in Artificial Intelligence analytics, cybersecurity, entrepreneurship, business transformation, and enterprise software. She has filed and has been issued over 13 key industry patents and is a Recurring Guest Lecturer at the University of California, Berkeley, and Merced, and most recently an Adjunct Professor at Southwest Law School.

1. Introduction Intent-based networking is the latest adoption of network orchestration and machine intelligence to automate the end-to-end flow of business requirements that translate into actual resolutions on the network [1, 2]. It starts with requirements wrapped into a formal language of intents to the realization of that intents in the network for sustained monitoring. Intent- based network orchestration with a centralized rule-based policy, shared knowledge objects, and effective logical segmentations combinedly work together to create a sustainable automation framework for effecting and visualizing business requisites onto a network. Automation of antenna tilt for optimal coverage using intent-based orchestration workflow is provided in Fig 1.

Fig.1 Intent-based Orchestration workflow
2. Existing intent-based network vs proposed framework Existing rule-based intent networking utilizes
the intents and orchestration frameworks for implementing a requirement on the network [1].
We have provisioned for agents that would continuously monitor the intents and network for changes.
Multiple machine learning prediction agents work in parallel to track changes in the network coverage
across the network. Any contradicting intents (i.e., one intent aims at increasing coverage and another
at decreasing at the same site.) are identified as part of the continuous monitoring process and sent
for evaluation. Closed-loop monitoring is provisioned to ensure the system receives feedback from the
network and reporting agents [3] which results in a lower risk of failures. The automation and analytics
enable faster detection of threats and aid in downtime reduction.
3. Proposed workflow and intent-based orchestration for Antenna Tilt Optimization As per Fig 1, the workflow
starts with the collection of requirements including parameters such as minimum possible tilt, maximum tilt,
signal frequency, traffic per cell, the existing location, the distance between stations, etc. Once the
required parameters are collected and an antenna tilt intent is generated. The antenna tilt intent is ingested
into the orchestration framework and the required data collection, and goal generation takes place. The intent
is realized in the network using agents such as grounding agents and deployment agents that are either automated
agents or a workflow-based which are defined in the Network Operation Center for a hardware amendment and are
monitored continuously. This offers a greater speed of execution and automation compared to existing frameworks of
rule-based systems.
4. Conclusion and future work The intent-based orchestration can easily optimize to execute antenna tilt action to
establish network coverage successfully. We are currently working on multiple intent resolutions using multiple
agent evaluations to perform concurrent deployments on the network.
References:
- https://tools.ietf.org/id/draft-clemm-nmrg-dist-intent-02.html
- Future Intent-Based Networking-On the QoS Robust and Energy Efficient Heterogeneous Software Defined Networks, Lecture Notes in Electrical Engineering, Eds. Mikhailo Klymash, Mykola Beshley, and Andriy Luntovskyy, Springer International Publishing, 2022.
- Taihyun Kim and E. H. Abed, "Closed-loop monitoring systems for detecting impending instability," in IEEE Transactions on Circuits and Systems I: Fundamental Theory and Applications, vol. 47, no. 10, pp. 1479-1493, Oct. 2000, doi: 10.1109/81.886978
Biography:
Principal Researcher – Ericsson Research AI ML Data Sciences and Quantum Computing Saravanan has got M.S. and PhD degrees in Computer Science and Engineering from Indian Institute of Technology Madras. He has a background in Research & Development in telecommunication business and other relevant areas with an experience of over 20 years.
He has been working with Ericsson for the past 11 years in Global Research division and filed more than 60 patents and published 100 research papers in various International Conferences and Journals. Attended and presented in many International Conferences and Research Forums. He has good experience in developing research prototypes relevant for customer business. His Interest in the fields of Data Mining, Text Mining, Information Retrieval, Mobile Social Network Analysis, IOT and Big Data Analytics, Fog computing, Neuromorphic and Quantum Computing. He has guided more than 100 research interns and mentored for PhD Scholars from different universities.

In path-protected spectrally-spatially elastic optical networks (SS-EONs), inter-core and inter-mode crosstalks (XTs)
are significant obstacles, which degrades the system performance [1-3]. XT-avoided and XT-aware approaches have been
used to overcome XT issues in path-protected SS-EONs. In the case of the XT-avoided approach, resource allocation is
not performed in neighboring modes and cores for different connections [2]. Whereas the XT-aware approach allocates
resources in neighboring modes and cores, but the induced XT must be less than or equivalent to the predefined XT
threshold limit [4].
In path-protected SS-EONs, the work in [4] introduced a shared backup path protection-based resource allocation model
considering inter-core and inter-mode XTs for offline SS-EONs. The introduced model presents two optimization problems
as integer linear programming (ILP), which are based on XT-avoided and XT-aware resource allocation, to minimize the
highest utilized spectrum slot index. However, the work in [4] considers the XT-avoided and XT-aware approaches only
in shared backup path-protected SS-EONs; the impact of XT-avoided and XT-aware approaches in dedicated path-protected
SS-EONs is not investigated. This work explores XT-avoided and XT-aware approaches in path-protection SS-EONs considering
both shared and dedicated protections.
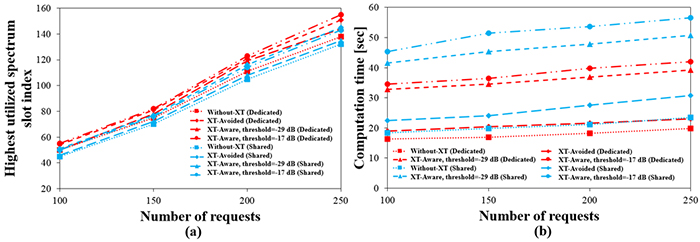
Fig.1 (a) Highest utilized spectrum slot and (b) computation time [sec] for NSFNET using different approaches.
For the performance evaluation, simulation settings are considered according to [4]. We obtain the results by using
heuristic approaches that consist of two phases. In the first phase, the primary and backup paths are determined for
each request. In the second phase, the primary and backup paths determined in the first phase are given as the input.
The requests are sorted in the decreasing order based on the demanded traffic, and they are placed in the network one
by one in a greedy manner for resource allocation.
Figure 1 shows the variation of the highest utilized spectrum slots and computation time [sec] with different numbers
of requests for different approaches. We observe that the shared protection provides better spectrum utilization compared
to the dedicated protection. The spectrum utilization is better for the XT-aware approach compared to the XT-avoided approach.
For the XT-aware approach, a higher XT-threshold improves the signal quality, but it reduces resource utilization.
On the other hand, a lower XT-threshold improves resource utilization, but it may degrade the signal quality.
It is also noticed that the computational time using the XT-avoided approach is smaller than that of the XT-aware approach.
References:
- H. Tode et al., “Routing, spectrum, and core and/or mode assignment on space-division multiplexing optical networks,” IEEE/OSA J. Opt. Commun. Netw., vol. 9, no. 1, pp. A99–A113, Jan. 2017.
- B. C. Chatterjee et al., “Priority-based inter-core and inter-mode crosstalk-avoided resource allocation for spectrally-spatially elastic optical networks,” IEEE/ACM Trans. Netw., vol. 29, no. 4, pp. 1634-1647, 2021.
- E. E. Moghaddam et al., “Crosstalk-aware resource allocation in survivable space-division-multiplexed elastic optical networks supporting hybrid dedicated and shared path protection,” IEEE/OSA J. Lightw. Technol., vol. 38, no. 6, pp. 1095–1102, 2020.
- J. Halder et al., “Shared backup path protection-based resource allocation considering inter-core and inter-mode crosstalk for spectrally-spatially elastic optical networks,” IEEE Commun. Lett., vol. 26, no. 3, pp. 637-641, 2022.
Biography:
Bijoy Chand Chatterjee is currently an Assistant Professor and a DST Inspire Faculty with South Asian University (SAU), New Delhi, and an Adjunct Professor with the Indraprastha Institute of Information Technology Delhi (IIITD), New Delhi, India since December 2018. Before joining SAU, he was an ERCIM Postdoctoral Researcher at the Norwegian University of Science and Technology (NTNU), Norway, a DST Inspire Faculty at IIITD, New Delhi, India, and a Postdoctoral Researcher in the Department of Communication Engineering and Informatics, the University of Electro-Communications, Tokyo, Japan. His research interests include optical networks, QoS-aware protocols, optimization, and routing. He has published more than 85 journal/conference papers. Currently, he has been serving as an associate editor in IEEE Access. He is a Fellow of IETE and a Senior Member of IEEE.

Signal transmission considering counter-propagation has been used to enhance resource utilization in spectrally
spatially elastic optical networks (SS-EONs) that utilize multi-core multi-mode fibers (MCMMFs) [1]. When a signal
is transmitted through MCMMFs, inter-core and inter-mode crosstalks are produced, suppressing resource utilization
to maintain transmission quality [2,3]. The crosstalk-avoided approach is one of the possible solutions to overcome
crosstalk issues. Therefore, the crosstalk-avoided approach and counter-propagation have jointly been considered to
enhance resource utilization while maintaining the crosstalk level. Taking this direction, the work in [4] presented
a bi-partitioning-based crosstalk-avoided resource allocation in SS-EONs to enhance resource utilization while suppressing
crosstalk, motivating us to present the impact of counter-propagation and bi-partitioning during resource allocation in
this work.
For performance evaluation, we consider three approaches, which are co-propagation resource allocation (CO) [3],
counter-propagation resource allocation with random bi-partitioning (CNT-RBP) [1], and counter-propagation resource
allocation with solving an optimization problem of bi-partitioning (CNT-OBP) [4]. The concept of counter-propagation
is shown in Fig. 1.
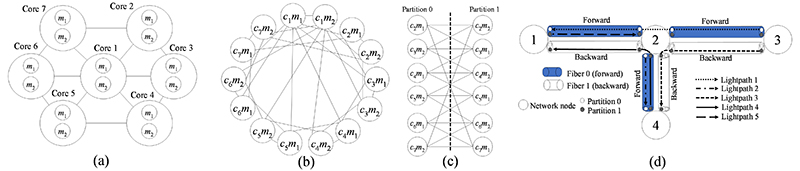
Fig.1 (a)Given core and mode adjacency of fiber structure, (b)auxiliary graph constructed using (a),
(c)bipartite graph to determine resources for counter-propagation, and (d)lightpath allocation using counter-propagation.
In CO, no partitioning for cores and modes is considered and the signal is propagated in the same direction of each fiber link. In CNT-RBP, we consider that signals are transmitted through counter-propagation. Using cores and modes, we create an undirected auxiliary graph; when the crosstalk between any two vertices of the auxiliary graph is larger than the auxiliary-threshold, two vertices are considered as adjacent, and an edge connects them. We randomly select a vertex from the auxiliary graph. Based on the selected vertex, we determine adjacent and non-adjacent vertex sets; these sets are distinct. During the determination of the sets, if any vertex is adjacent to any vertex of both distinct sets, we eliminate that vertex and do not consider it for resource allocation. In each fiber, the adjacent vertices transmit signals for different directions, which means alternating the propagation direction of adjacent vertices; non-adjacent vertices transmit signals in the same directions in each fiber. In CNT-OBP, we adopt a bi-partitioning optimization problem with vertex elimination to maximize the number of non-adjacent cores and modes in each partition of the bipartite graph; two distinct sets of cores and modes are used in a counter-propagation manner for lightpath allocation.
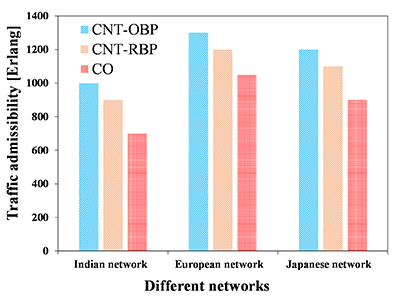
Fig.2 Traffic admissibility using different approaches under 1% blocking of requests.
For the performance evaluation, simulation settings are considered according to [4]. Figure 2 observes that CNT-OBP accommodated 42.86%, 23.81%, and 33.33% more traffic than that of CO for the Indian, European, and Japanese networks, respectively, under 1% blocking of requests in the network.
References:
- F. Tang et al., “Crosstalk-aware counter-propagating core assignment to reduce inter-core crosstalk and capacity wastage in multi-core fiber optical networks,” IEEE/OSA J. Lightw. Technol., vol. 37, no. 19, pp. 5010–5027, 2019.
- F. Arpanaei et al., “Three-dimensional resource allocation in space division multiplexing elastic optical networks,” IEEE/OSA J. Opt. Commun. Netw., vol. 10, no. 12, pp. 959–974, Dec. 2018.
- B. C. Chatterjee et al., “Priority-based inter-core and inter-mode crosstalk-avoided resource allocation for spectrally-spatially elastic optical networks,” IEEE/ACM Trans. Netw., vol. 29, no. 4, pp. 1634-1647, 2021.
- B. C. Chatterjee et al., “BPRIA: Crosstalk-avoided bi-partitioning-based counter-propagating resource identification and allocation for spectrally-spatially elastic optical networks,” IEEE Trans. Netw. Serv. Manag., 2022 [to appear].
Biography:
Bijoy Chand Chatterjee is currently an Assistant Professor and a DST Inspire Faculty with South Asian University (SAU), New Delhi, and an Adjunct Professor with the Indraprastha Institute of Information Technology Delhi (IIITD), New Delhi, India since December 2018. Before joining SAU, he was an ERCIM Postdoctoral Researcher at the Norwegian University of Science and Technology (NTNU), Norway, a DST Inspire Faculty at IIITD, New Delhi, India, and a Postdoctoral Researcher in the Department of Communication Engineering and Informatics, the University of Electro-Communications, Tokyo, Japan. His research interests include optical networks, QoS-aware protocols, optimization, and routing. He has published more than 85 journal/conference papers. Currently, he has been serving as an associate editor in IEEE Access. He is a Fellow of IETE and a Senior Member of IEEE.

Techniques that use wide area networks to guarantee the delivery of large data sets within a pre specified deadline have attracted attention in scientific computing and large scale data centers (hereafter, such data transfer is referred to as "deadline aware data transfer"). Scheduling deadline aware data transfer at the originating node is done in slots with fixed length cycles ranging from 100 ms to several seconds. At the beginning of each slot, the most appropriate job to transfer in that slot is selected from among several waiting jobs to keep the deadline. Once a job is selected for that slot, the data for that job is packetized and transferred to the output line. Scheduling deadline aware data transfer s jobs in the presence of high priority traffic is not easy (Fig.1). To meet all requirements by the deadline, the future situation must be accurately known and job scheduling must be optimally distributed over the time axis, and this problem can be formulated as an optimization problem. The optimization problem must be run iteratively each time a new job arrives, but in solving each optimization problem, only limited knowledge about the future is available, meaning that the answers to the solved optimization problems may be wasted in the future. Instead of taking the approach of solving such optimization problems sequentially over and over again, this study examines the use of reinforcement learning to determine the optimal action to take depending on the state of the system. Reinforcement learning learns how to schedule the most rewards through a series of actions. Reinforcement learning has been successful in environments with deterministic behavior because it is possible to iteratively learn episodes and find ways to improve the rewards obtained. However, the challenge in this study is that the behavior of the environment is stochastic The issue here is whether scheduling can be done well for job arrival patterns that are not in the learned episodes, and it is not possible to schedule correctly for jobs with more severe arrival patterns than those in the learned episodes. It is not clear what arrival patterns make scheduling difficult. Therefore, the objective of this study is to identify learning episodes for applying reinforcement learning to problems in which the environment changes randomly. In this talk, we will survey the work done in both the areas of deadline aware job scheduling and reinforcement learning, and discuss future directions for applications of reinforcement learning in stochastic environments.
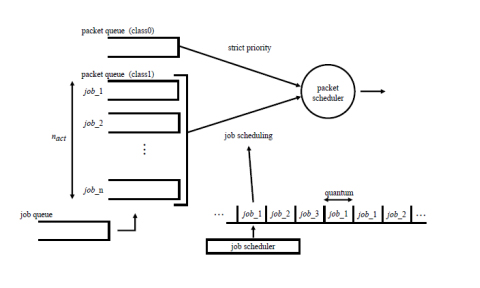
Fig.1 Deadline-aware Job Scheduling
Biography:
Kohei Shiomoto is a Professor, Tokyo City University, Tokyo Japan. Since joining NTT Laboratories in 1989, he has been engaged in research and development in the data communications industry on high-speed computer network architecture, traffic management, and network analysis to create innovative technologies for the Internet, mobile, and cloud computing. From 1996 to 1997, he was a visiting scholar at Washington University in St. Louis, MO, USA. In 2017, he joined Tokyo City University to engage in research and education on data science and computer networking. Current research interests include data mining for network management, human flow analysis, cloud computing and blockchain. He has published more than 70 academic papers, 130 refereed international conference papers, and 6 RFCs in IETF. He served as Guest Co-Editor for a series of special issues established in IEEE Transactions on Network and Service Management. He has served in various roles organizing IEEE ComSoc conferences including IEEE NOMS, IEEE IM, and IEEE NetSoft. He served as the lead Series editor for the Network Softwarization and Management Series in IEEE Communications Magazine, 2018-2021. He is Fellow of the IEICE, Senior Member of IEEE, and a member of ACM and IPSJ.

Biography:
Yoshiaki Sone, Senior research engineer in NTT. He received M.E. degrees in electronics engineering from Tohoku University, Miyagi, in 2003. In 2003, he joined NTT lab and has been engaged in research on network engineering technologies for optical transport networks and related standardization.From 2017 to 2021, he also worked as field application engineer at NTT electronics America from 2017 to 2021.

Biography:
Olivier Renais received his master‘s degree of Optronics in 1992 from the E.N.S.S.A.T Lannion. He has been working as a System Engineer in Pirelli and CISCO Systems, as a consultant in NORTEL, and joined Orange Labs Lannion in 2005 as an optical network architect. He is currently involved in OpenROADM and transportPCE, an OpenDaylight project which provides a reference implementation for the control of OpenROADM based optical infrastructure.

Biography:
Balagangadhar (Bala) Bathula received the Ph.D. degree in electrical communication engineering from the Indian Institute of Science, Bangalore, India. He is currently working as a Principal Member of the Technical Staff, Network Cloud and Infrastructure and Services, AT&T Labs, USA. Before joining AT&T, he worked as a Postdoctoral Researcher with the Department of Electrical Engineering, Columbia University, New York. He is leading the activities of OpenROADM Multi-Source Agreement (MSA) (disaggregated transport layer). His research interests are in software-defined networks (SDNs), open architectures for transport, cross-layer network architectures, backbone network design, network cost optimization, optical networks and telemetry, and machine learning. He served as a reviewer for many IEEE/OSA conferences/journals. He has published several articles in optical networks and holds 10 patents.
Satoshi Yamanoi, OA Laboratory Co. Ltd., Japan
Ryo Nishimura, TOYO Corporation, Japan
Shin'ichi Akahane, ALAXALA Networks Corp., Japan
Yusuke Hirota, NICT, Japan
Masaki Murakami, Keio University, Japan

Biography:
Ved P. Kafle is a research manager at National Institute of Information and Communications Technology (NICT), and concurrently holding a visiting associate professor's position at the University of Electro-Communications, Tokyo. He holds a B.E. (Honours) degree in Electronics and Communications from Punjab Engineering College, India, an M.S. degree in Computer Science and Engineering from Seoul National University, South Korea, and a Ph.D. degree in Informatics from the Graduate University for Advanced Studies, Japan. He has been serving as a Co-rapporteur of ITU-T Study Group 13 since 2014. His current research interests include network architectures, beyond 5G networks, and network service automation by AI and machine learning. He is a fellow of ITU-T SG13 and a senior member of IEEE.

Biography:
Dr Antonio Skarmeta received the M.S. degree in Computer Science from the University of Granada and B.S. (Hons.) and the Ph.D. degrees in Computer Science from the University of Murcia Spain. Since 2009 he is Full Professor at the same department and University. Antonio F. Skarmeta has worked on different research projects in the national and international area in the networking, security and IoT and 5G area, and now is involved in 5GInspireplus, 5GMobix, GN4+, CyberSec4Europe and BIECO. He coordinated the H2020 project IoTCrawler focusing on IoT advanced discovery on IPv6 networks and OLYMPUS on privacy preserving IdM and now the 6G project CERBERUS on Security on Beyond 5G. He has been chair of several conference and workshop, with special attention to IEEE 5GWF and now the IEEE Future Networks World Forum.
His main interested is in the integration of 5G, security services, identity, IoT and Smart Cities, being scientific manager of the Smart City project of Murcia City Hall (MiMurcia). He has been the head of the research group ANTS since its creation on 1995. Actually, he is also advisor to the vice-rector of Research of the University of Murcia for International projects and head of the International Research Project Office. Since 2014 until 2010 he has been Spanish National Representative for the MSCA within H2020. He has published over 200 international papers and being member of several program committees.